Strengthening the Cyber Resilience of a Renewable-Heavy Grid
Threats to America’s electric energy infrastructure are intensifying and increasingly diverse. In part, this trend reflects the sophisticated new attack capabilities that potential adversaries are developing. But a second factor is also altering the threat landscape. The transformation of the U.S. grid is creating novel opportunities for adversaries to attack our electric system. Yet, if we can secure the devices that are driving this transformation, we can also adopt innovative strategies to strengthen grid resilience and directly counter the objectives that potential adversaries will seek to achieve in attacking our electric system.
The Rise of Inverter-Based Resources: Implications for Cybersecurity
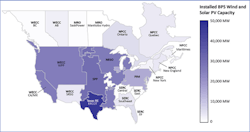
The grid is rapidly incorporating solar, wind, and battery energy storage systems on a nationwide basis. These assets are inverter-based resources (IBR): they rely on inverters and other power electronics to deliver the electricity they generate to the grid. In particular, inverters convert direct current (DC) electricity, which is what solar panels generate, to alternating current (AC) electricity, which is what the grid uses. In a June 2023 document, the North American Electric Reliability Corporation (NERC) states that “inverter-based resources are now found everywhere across the bulk power system (BPS) in North America and are the most significant driver of grid transformation today.”
These threats go beyond local distribution systems, however. As inverter-based resources are increasingly tied to the high-voltage transmission infrastructure that provides the backbone of America’s grid, the systemic deficiencies of IBRs will pose growing risks to the US electric system as a whole.
Dramatic Increases in Solar and Wind Power Generation
Today, the severity of this threat is limited by the relatively small portion of U.S. electricity that solar and wind generation provides. Solar photovoltaic and wind systems combined provided only 13.6% of the electricity generated in 2022. However, those levels are projected to quickly increase. According to an April 2023 report from DOE’s Lawrence Berkley National Laboratory, the combined solar and wind capacity now actively seeking grid interconnections (~1,250 GW) approximately equals the installed capacity of the entire U.S. power plant fleet.
DOE also projects rapid growth in DER generation. Approximately 90 GW of DER were deployed across the grid in 2022, half of which are rooftop solar installations that now total over 3 million systems. DOE expects those deployments to quadruple by 2025 to approximately 380 GW. Changes in federal and state renewable energy targets, constraints on transmission system availability and expansion, supply chain problems, and other factors could limit the expansion of solar and wind generation in the coming decade. Nevertheless, strategies to secure the grid of the future must account for massive increases in IBRs and the new attack surfaces they will create.
These strategies should also account for the emerging capabilities that inverters and other power electronics will offer – for good and ill. Efforts are underway to enable IBRs to help operators
maintain the grid’s reliability, including by controlling frequencies and voltages when disturbances occur.
Reliability vs. Resilience?
As inverter-based resources provide an increasing share of U.S. power, their ability to provide such reliability services will become vital. Battery energy storage system (BESS), which also rely on inverters, will be especially important for future reliability because they can help grid operators deal with the intermittency of solar and wind-provided power and provide additional frequency and voltage support when needed. On Oct. 18, 2023, the Federal Energy Regulatory Commission (FERC) directed the North American Electric Reliability Corporation (NERC) to develop standards to help ensure that IBRs provide such essential reliability services and fill gaps in past inverter performance.
But these advanced capabilities also entail risks. As DOE warns, adversaries can seek to access and manipulate advanced IBR capabilities, and use them to create potentially catastrophic disruptions. The very measures we take to enhance the reliability of an IBR-heavy grid may inadvertently jeopardize the grid’s cyber resilience. Subsequent sections of this article propose options to mitigate these risks and make the future grid both reliable and survivable.
On a larger scale, grid strategies should also capitalize on the novel security benefits that the nationwide deployment of IBRs could provide. If we can secure solar, wind, and battery storage systems from adversary disruption and exploitation, we may be able to adopt new grid protection and emergency response strategies that help prevent China or other adversaries from achieving their objectives. We can also explicitly structure our implementation of these new strategies to strengthen deterrence by resilience, and (in combination with credible threats of responding to enemy attacks) help convince Xi Jinping that the benefits of striking the U.S. grid are dwarfed by the costs China would incur.
Opportunities To Bolster Grid Security: Nationwide, Regional, And Device-Level Options
As millions of solar, wind, energy storage, and control systems are deployed throughout the U.S., we may be able to shift toward a decentralized grid architecture that is more difficult to disrupt than today’s version, which relies on a small number of critical, high value assets that adversaries can selectively target. Protecting those assets remains absolutely vital. Yet, if we also widely disperse IBR generation and control systems, we can greatly complicate adversary attack planning and execution – as long as those systems can themselves survive enemy disruption and misoperation.
At a regional scale, where individual transmission operators (TOPs), balancing authorities, and reliability coordinators help operate the BPS, dispersed generation can also enable new strategies to limit the impact of grid instabilities and cascading blackouts. Microgrids already enable the creation of “power islands” that can segment from the grid in emergencies to sustain service to military bases and other customers within them. Now, building on existing transmission system emergency plans, dispersed generation may enable grid operators and their partners to create much larger (and, ideally, more stable) emergency islands that can power the multiple, interdependent infrastructure systems on which national security, public safety, and the grid itself depend.
At the device level, the future deployment of grid-forming inverters, advanced controls for battery energy storage systems (BESS), and other emerging technologies may enable TOPs to conduct power restoration using decentralized assets that will be more difficult for adversaries to target and disrupt. These restoration opportunities could have special strategic value if China or other adversaries conduct sustained, multi-week grid attacks during regional conflicts with the United States.
In addition, U.S. resilience strategies should account for a further challenge to grid reliability and resilience: the rise of electric vehicles (EVs), “smart” buildings, and other highly controllable sources of demand for power. Electric system operators must constantly maintain the balance between total generation and the consumption of electricity, or load. Such balancing operations are crucial to maintain or restore grid reliability when disturbances occur - including, potentially, cyber-induced disruptions.
Grid operators often respond to imbalances by conducting demand-side management operations. For example, they can conduct load shedding, and temporarily halt or reduce the flow of power to selected areas or customers. With the rapidly growing deployment of EVs and their charging stations, as well as other loads that can be controlled via the internet, options are now emerging for emergency demand-side management on a massive scale. These same capabilities could give advesaries unprecedented opportunities to manipulate demand for power, and exacerbate rather than remedy grid instabilities.
Prioritizing And Implementing Grid Resilience Initiatives
With the emergence of so many new attack surfaces, developing and implementing grid resilience strategies will entail an additional challenge: prioritizing our cybersecurity efforts. DOE offers a starting point to do so. The Department recommends that cyber resilience initiatives concentrate on potential threats “where cyber manipulation could result in unacceptable consequences.” That recommendation offers a valuable starting point to focus our resilience initiatives. In addition, we should prioritize our efforts to prevent Chinese leaders from accomplishing their goals in attacking the grid.
U.S. intelligence assessments and DOD’s 2022 National Defense Strategy suggest that China will have two especially prominent goals in disrupting U.S. infrastructure. First Chinese leaders will seek to undermine the will of the U.S. public to defend our allies abroad. Jeopardizing public safety by halting the flow of power to water systems, hospitals, and other electricity-dependent “lifeline” facilities offers a highly leveraged means to achieve that goal, and coerce U.S. leaders into backing down in confrontations over Taiwan or other regional conflicts. U.S. grid strategies should help prevent Chinese leaders from accomplishing such objectives. In particular, as inverter-based resources become ubiquitous, we should prioritize efforts to secure them so they can help protect (and, if necessary, rapidly restore) power to facilities and functions essential for saving American lives.
Chinese leaders may also conduct much more limited strikes that might entail reduced escalatory dangers, but still help them prevail in regional conflicts. Senior U.S. officials and military officers warn that Beijing may launch narrowly targeted attacks on the grid to disrupt the domestic operations necessary to support military power projection during an intensifying confrontation over Taiwan or some other regional contingency. Grid security strategies for the IBR-heavy grid must also help strengthen resilience against such “fort to port” attacks and other efforts to impede US preparations at home for warfighting abroad.
The prerequisite for achieving both goals: as the U.S. transitions from a relatively small number of large-scale generators to a highly decentralized system, we need to prevent those dispersed resources and their control systems from having common mode failures that would enable Beijing to manipulate or disrupt them at whatever scale Chinese leaders desire – from key U.S. ports of debarkation to comprehensive, nationwide strikes.
We need device-level security requirements for inverters and other grid components that pose special risks of exploitation for catastrophic or more targeted attacks. We should also develop measures to secure the grid against large-scale load manipulation, and leverage America’s rapidly increasing battery storage capabilities to help protect and rapidly restore power to the facilities that Chinese leaders seek to hold at risk.
Many such initiatives will require new regulatory strategies. The BPS has mandatory, enforceable cybersecurity standards that strengthen its resilience against attack. No equivalent standards exist for distribution-level utilities, which are regulated by states and which are incorporating rapidly expanding solar generation assets and control systems. Moreover, energy aggregators and other non-utility operators play increasingly important roles in managing and marketing these distribution-level power flows. These new entrants typically have far less cybersecurity experience and expertise than their utility counterparts.
We should develop a holistic regulatory strategy that includes all of the assets and participants needed to prevent high-consequence events, including demand-side attacks. I also recommend that we establish mandatory, enforceable cybersecurity standards for all grid components that China might exploit to conduct attacks that would jeopardize public safety or national security, regardless of whether those components are deployed on distribution systems or the BPS.
Since my July 18, 2023 testimony before the Oversight and Investigations Subcommittee of the U.S. House of Representatives Committee on Energy and Commerce, the deployment of IBRs has continued apace. That shift towards potentially vulnerable generation makes the need all the greater for the establishment of device-level security requirements for inverters and other grid components that pose special risks of exploitation for catastrophic or more targeted attacks. We also need to accelerate the development of measures to secure the grid against large-scale load manipulation, and leverage America’s rapidly increasing battery storage capabilities to help protect and rapidly restore power .
If we can strengthen the protection of IBRs, we may be able to adopt new resilience strategies that leverage their highly dispersed deployment. Such strategies could offer immense benefits for national security. In addition, we can focus strategies to directly counter the objectives that China and other potential adversaries are likely to seek if they attack America’s electric system, and -through deterrence by resilience – ultimately make such attacks less likely to occur.
Dr. Paul N. Stockton is a Senior Fellow of the Johns Hopkins University Applied Physics Laboratory, and is President of Paul N Stockton LLC, a strategic advisory firm in Santa Fe, NM. He has published numerous reports for industry and government leaders on critical infrastructure resilience and national security.
Dr. Stockton chairs the Homeland Defense Subcommittee of DOD's Reserve Forces Policy Board. He also chairs the Grid Resilience for National Security Subcommittee of the Department of Energy's Electricity Advisor Committee. In addition, he is Chair of the Board of Directors of Analytic Services, Inc., and serves on advisory boards for the Idaho National Laboratory and other organizations.
Dr. Stockton served as the Assistant Secretary of Defense for Homeland Defense and Americas’ Security Affairs from June, 2009 until January, 2013. He subsequently served from 2013-2020 as Managing Director of Sonecon LLC in Washington, DC. Prior to his tenure as Assistant Secretary, Dr. Stockton was a Senior Research Scholar at Stanford University’s Center for International Security and Cooperation. He also served as Associate Provost of the Naval Postgraduate School, where he founded the Center for Homeland Defense and Security (CHDS) and the Center for Civil-Military Relations. He was a Legislative Assistant for defense and foreign policy for Senator Daniel Patrick Moynihan and a Research Associate at the International Institute for Strategic Studies.
Dr. Stockton was twice awarded the Department of Defense Medal for Distinguished Public Service, DOD’s highest civilian award. In addition, the Department of Homeland Security awarded Dr. Stockton its Distinguished Public Service Medal.
About the Author
Paul N. Stockton
Dr. Paul N. Stockton, a Senior Fellow at Johns Hopkins University Applied Physics Laboratory and President of Paul N Stockton LLC, a strategic advisory firm in Santa Fe, NM., has published numerous reports to industry and government clients on critical infrastructure resilience and national security.
Dr. Stockton chairs the Homeland Defense Subcommittee of DOD's Reserve Forces Policy Board. He also chairs the Grid Resilience for National Security Subcommittee of the Department of Energy's Electricity Advisor Committee. He served from 2013-2020 as Managing Director of Sonecon LLC in Washington, DC. Before joining Sonecon, Dr. Stockton served as the Assistant Secretary of Defense for Homeland Defense and Americas’ Security Affairs from June, 2009 until January, 2013.
Prior to his tenure as Assistant Secretary, Dr. Stockton served as Senior Research Scholar at Stanford University’s Center for International Security and Cooperation. He also served as Associate Provost of the Naval Postgraduate School, where he founded the Center for Homeland Defense and Security (CHDS) and the Center for Civil-Military Relations. He was a Legislative Assistant for defense and foreign policy for Senator Daniel Patrick Moynihan and a Research Associate at the International Institute for Strategic Studies.
Dr. Stockton serves on the Board of Directors for Analytic Services Inc., and on advisory boards for the Idaho National Laboratory and other organizations.
Dr. Stockton was twice awarded the Department of Defense Medal for Distinguished Public Service, DOD’s highest civilian award. In addition, the Department of Homeland Security awarded Dr. Stockton its Distinguished Public Service Medal.