Cyber security protects all aspects of critical infrastructure.
Cyber security is an integral part of ABB's products and systems. It is addressed at every phase, from design and development to maintenance and support of the product. Threat modeling and security design reviews, security training of software developers, as well as in-house and external security testing as part of quality assurance processes, are examples of the numerous steps ABB is taking to increase the reliability and security of its solutions.
Cyber security embedded in the product life cycle
ABB was, for instance, the first SCADA (Supervisory Control and Data Acquisition) vendor to partner with the US Department of Energy's Office of Electricity Delivery and Energy Reliability through its National SCADA Test Bed program at Idaho National Labs. Work began in 2003 to perform cyber security assessments for ABB's Network Manager SCADA/energy management system (EMS) product. Results from that initiative led to many security upgrades and improvements.
One very important initiative within ABB is the Device Security Assurance Center (DSAC). The objective of the DSAC is to provide independent and continuous protocol- stack robustness and vulnerability assessments of embedded devices as part of the development process. The test center utilizes a suite of state-of-the-art open-source, commercial and proprietary solutions, and the testing scope includes device profiling, known vulnerability scanning, and protocol fuzzing. The DSAC currently performs more than 100 tests per year, helping ABB to continuously improve the robustness and resilience of embedded devices.
1 Cyber security safeguards against unauthorized local as well as remote malicious access to control rooms.
Examples of the improvement of cyber security capabilities include the recent releases of ABB's Extended Automation System 800xA, which has a substantial set of security capabilities to support the secure operation of process automation solutions. These capabilities include support for third-party malware (ie, malicious software) protection solutions (antivirus as well as application whitelisting), granular access control (flexible account management as well as granular access permissions and role-based access control), and secure communication using IPsec (ie, Internet Protocol security) ➔ 1. However, the security considerations are not limited to system capabilities, as they also include support during the product life cycle; eg, providing validation of third-party security updates and a firm process for vulnerability handling.
Another example of the company's efforts to improve cyber security is the RTU560, widely used as a classical, substation automation, smart-grid and feeder RTU (remote terminal unit), or as a gateway. Its security capabilities address the market needs induced by NERC CIP (North American Electric Reliability Corporation Critical Infrastructure Protection1) compliance and address industry standards such as IEC 62351 and IEEE 1686. The capabilities include granular access control (including role-based access control), logging and reporting of security events (locally or to an available Security Information and Event Manager, or SIEM) and support for secure tunneling of communications through an integrated IPsec VPN client. The product life cycle is of course not limited to product capabilities and the support of products, but it also encompasses the secure delivery of projects. An excellent example in which cyber security was integrated throughout the project life cycle is the development of Norske Shell's Ormen Lange gas field and Draugen offshore platform ➔ 2.
2 Safe remote access through ABB Service Desk
Cyber security embedded in the organization
ABB has identified cyber security as a strategic initiative and therefore established a formal cyber security organization led by the ABB Group Cyber Security Council. The council ensures a continuous strengthening of ABB's operational readiness and actively works to maintain the internal cyber security awareness and expertise throughout the company. The ABB cyber security organization comprises experts from various backgrounds including R&D, IS infrastructure, legal and communications in order to properly address the multifaceted challenges of cyber security. In addition, ABB complements and enhances its internal expertise and scope not only through collaborations with customers and government organizations but also through a strategic partnership with Industrial Defender, a company dedicated to ensuring the availability, reliability and security of critical infrastructure.
The future of industrial-control-system cyber security is comparable to the enterprise IT domain, where security has become a part of daily life with automated software updates, security patches and antivirus updates in order to thwart a growing number of threats. ABB is prepared to constantly enhance the security features of its offerings through technological advances and organizational readiness so it can continue to provide products and services that meet the security needs of its customers' critical infrastructure.
3 ISA99 / IEC 62443
Collaboration across industry
To establish a high industry-wide cyber security level, standards are required. Standardization initiatives by IEEE, IEC and ISA were established with ABB playing an active role in defining and implementing cyber security standards for power and industrial control systems ➔ 3. The main objective of these initiatives is to establish and maintain the necessary levels of cyber security, while preserving the availability and functional interoperability of systems. In addition, ABB has participated in EU projects, eg, ESCoRTS and VIKING , and continues to invest in initiatives that bring together all stakeholders, including private companies, governments, academia and other research organizations.
ESCoRTS
ESCoRTS2 was a joint endeavor among EU process industries, utilities, leading manufacturers of control equipment, and research institutes to foster progress toward the cyber security of control and communication equipment in Europe. It addressed the need for standardization and developed a dedicated roadmap for standardization and research directions.
ESCoRTS has been a leading force for:
- Disseminating best practice on security of SCADA systems
- Hastening and ensuring convergence of SCADA standardization processes worldwide
- Paving the way to establishing cyber security testing facilities in Europe
The ESCoRTS project included a field evaluation of the available cyber security standards. ABB and the Italian energy utility ENEL jointly performed a cyber security assessment of an ENEL power generation plant that was redesigned in 2003. The assessment was based on the current status of the IEC 62443 standard at the time. The results included a positive assessment of the standard's applicability and utility in securing an industrial control system and also demonstrated that, with the commitment of and collaboration among the vendor, system integrator and asset owner/ operator, an industrial control system's security posture can be improved within cost and resource constraints typically applicable to existing plants.
4 Cyber security is an essential component in today’s power grids, enabling a reliable supply of power by protecting against attacks.
VIKING
VIKING3 was a cyber security project that investigated vulnerabilities in state-of-the-art SCADA systems used for the supervision and control of electrical grids ➔ 4. The VIKING consortium was led by ABB and consisted of members from utilities, industry and academia. The objectives of VIKING were to:
- Develop calculation models for SCADA system security
- Estimate the societal costs and consequences of blackouts generated by failing SCADA systems
- Propose mitigation strategies for the vulnerabilities identified
These objectives were fulfilled by developing a security analysis language and a virtual society model, and by investigating vulnerabilities in power applications and proposing countermeasures for these vulnerabilities. The results have been summarized in a number of story boards where possible cyber attacks on SCADA systems are described, and they include the likelihood of success for these attacks as well as their social and economic impact. Also included are possible mitigation methods and their potential to improve security.
An ongoing research topic
Collaboration with reputable universities is also a key element of ABB's research strategy. In 2006, eg, ABB began a three-year research project, "Threat Modelling," in cooperation with the University of St. Gallen and the Swiss Commission for Technology and Innovation (CTI). In this project, a methodology for threat modeling of embedded devices was successfully developed. The methodology allows for assessment and documentation of the actual security of the developed system throughout product development [1, 2]. On several occasions this methodology has been used within ABB to conduct security assessments as part of the development process.
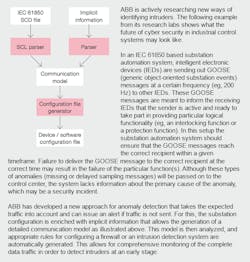
ABB is committed to technology leadership and significantly invests in internal research as well – looking at, for instance, new innovative ways to protect industrial control systems [3,4]. ABB has and continues to address current and future needs by developing new approaches for cyber security in industrial control system. Examples include novel approaches for anomaly detection ➔ 5 and the design of authentication architectures that allow the use of a single password per user throughout a complete plant.
5 Research case study: Advanced Anomaly Detection and Security Configuration (ANADS)
For more information about cyber security at ABB, please visit www.abb.com/cybersecurity or email [email protected].
----------------
Footnotes
1 See www.nerc.com
2 See www.escortsproject.eu
3 See www.vikingproject.eu
References
[1] Köster, F., Nguyen, H. Q., Klaas, M., Brändle, M., Obermeier, S., Brenner, W., Naedele, M. (2009, April). Information security assessments for embedded systems development: An evaluation of methods. 8th Annual Security Conference, Las Vegas, United States.
[2] Köster, F., Nguyen, H. Q., Brändle, M., Obermeier, S., Klaas, M., Brenner, W. (2009, April). Collaboration in security assessments for critical infrastructures. 4th International CRIS Conference on Critical Infrastructures, Linköping, Sweden.
[3] Brändle, M., Koch, T. E., Naedele, M., Vahldieck, R. Strictly no admittance: Keeping an eye on IT security in the plant. ABB Review 1/2008, 71–75.
[4] Naedele, M., Dzung, D., Stanimirov, M. (2001, September). Network security for substation automation systems. Safecomp 2001, Budapest, Hungary.
----------------
Sebastian Obermeier
Sascha Stoeter
ABB Corporate Research, Industrial Software Systems
Baden-Dättwil, Switzerland
[email protected]
[email protected]
Ragnar Schierholz
Markus Braendle
ABB Group Cyber Security Council
Zurich, Switzerland
[email protected]
[email protected]