Part of the nature of our industry’s defenses against cybersecurity threats is that personnel involved in the protection of our nation’s critical infrastructure typically try to maintain a relatively low profile instead of shouting out about details of their work.
In his excellent July 7, 2017, Energy Times story, “Wolf Creek Nuclear Plant Hit by Cyberattack,” Marty Rosenberg interviewed cybersecurity leaders, and reviewed related, official, emailed statements regarding the recently publicized event.
I found Marty’s reference to Ted Koppel’s 2015 book, Lights Out very helpful. Ted Koppel wrote: “There is, as yet, no real sense of alarm attached to the prospect of cyber war,” and added “for the first time in the history of warfare, governments need to worry about force projections by individual laptop.”
Ted Koppel, I beg to differ with you on this one! The sense of alarm about defending our grid was well in place long before your book was written.
Isn’t it overwhelmingly obvious that utility personnel will avoid publicizing anything that would help our enemies, or sensationalize the threats we face?
This obviousness makes me wonder exactly where the “lights” are “out.”
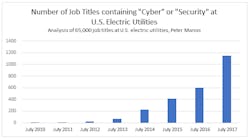
Instead of engaging in additional sarcasm, I decided to create the following simple snapshot using real data, showing how our industry has not been sitting on its hands, while also not giving the terrorists any information of value. In this chart, I took a decent-sized sample of contacts in our industry, in which I analyzed job titles from more than 65,000 utility personnel at large U.S. electric utilities, and did a quick sort based on the number of those jobs that contained “cyber security” in the job title.
This little study is not to be considered a complete rendering of the number of utility personnel involved in this work, since it is quite likely some of the most important players may have nothing in their job titles indicating their involvement in cybersecurity. Aside from violinists, few of us like to lead with the chin.